IT Notice – Increase in ClickFix Social Engineering Attacks
The Security Operations team has noticed a recent increase in social engineering attacks referred to as “ClickFix” in the McMaster community.
In many cases, websites use “Completely Automated Public Turing tests to tell Computers and Humans Apart,” commonly known as CAPTCHAs, for legitimate purposes to determine whether a visitor is an automated bot or a real person.
In ClickFix attacks, attackers compromise websites to display a fake CAPTCHA. These attacks attempt to convince users to run malicious commands on their computers, typically using PowerShell scripts through the Windows Run dialog box, Windows Terminal, or Windows PowerShell.
The image below shows an example of a ClickFix attack using a fake CAPTCHA prompt that attempts to trick users into opening PowerShell and executing a malicious command.
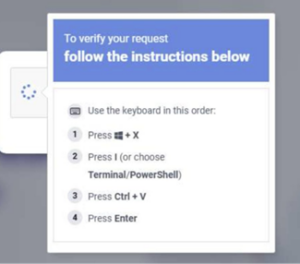
These prompts may appear in different forms depending on the source, such as on websites (as CAPTCHA prompts or malicious advertisements), in Microsoft Word documents, or in phishing emails.
The Security Operations team is advising the McMaster community to be cautious of requests to use the Windows Run dialog box (e.g. Windows Key + R or Windows Key + X) to copy and paste code into Windows.
If a website, CAPTCHA, email, or Microsoft Word pop-up asks you to press the Windows Key + R or to open PowerShell and paste and run code, it’s highly likely that this is a malicious “ClickFix” social engineering attack.
Please report all suspicious messages to is-spam@mcmaster.ca
References:
- https://x.com/MsftSecIntel/status/2029692925118992473
- https://www.microsoft.com/en-us/security/blog/2025/08/21/think-before-you-clickfix-analyzing-the-clickfix-social-engineering-technique/
Related News
News Listing

Women in Tech: Spring 2026 Series Highlights McMaster Leaders Shaping the Future of Technology
News Category
March 6, 2026
Innovation Meets Leadership: McMaster and Cisco Spotlight Women’s Health and Technology
News Category
November 6, 2025

